SecTrail Certificate Manager

SecTrail CM is used to manage digital certificates used by active devices and servers running on Data Networks for TLS/SSL protocols.
SecTrail CM handles the digital certificate management itself without the need for human factor intervention. This operation is currently done manually in many institutions and companies, causing them many disadvantages and waste of time.
| Virtual Appliance Requirements |
|
| Discovery |
|
| SSL Certificates |
|
| Sertifika Otoriteleri(CA) |
|
| Otomasyon |
|
| Integration |
|
| Automation Workflows |
|
| Certificate Integration |
|
| Logging and Reporting |
|
| Alarm Generation and System Analysis |
|
| Multi-Device Integration |
|
- Technical Datasheet
-
Virtual Appliance Requirements - Hypervisor Platforms : Vmware Vsphere/ESXi, Hyper-V
- Minimum Hardware Requirements : 4 vCPU, 8GB RAM, 100GB HDD, 1GBit NIC
- Operating System : Linux 8
- Supported Authentication Methods: Active Directory/LDAP, LocalDB
- Management Interfaces : HTTPS (GUI), SSH (CLI)
- Logging and Alarm Methods : E-Mail, SNMP, Syslog
- Redundancy : Active-Active Clustering
Discovery - Network Discovery (IP/CIDR)
- Discover from API
SSL Certificates - Extended Key Usage : serverAuth, clientAuth, codeSigning, emailProtection, timeStamping, OCSPSigning, IPSecIKE, msCodeInd, msCodeCom, msCTLSign, msEFS
- Types : RootCA, SubCA, Self-Signed, CSR, Issued
- Format : CRT, PEM, CSR, PKCS12
- Key Bits : 1024, 2048, 4096, 8192
- Key Algorithms : RSA, EC
- Storage Types : Encrypted DB, HSM
Sertifika Otoriteleri(CA) - LocalCA
- ADCS
- GlobalSign
Otomasyon - F5 BIG-IP – VS Discovery and SSL certificate deployment
- Microsoft IIS – VHost Discovery and SSL certificate deployment
- Apache – VHost Discovery and SSL certificate deployment
Integration - Cyberark Vault – Password and certificate/key upload
- Maximo – Data feed, Task Automation
- ARX – Key upload
- IBM Datapower – Monitor/Alarm certificate store with API communication
- Features
-
Automation Workflows - Automating your business processes,
- Creating workflow processes in line with your own needs,
- Automate your own tasks by creating and scheduling.
Certificate Integration - Determining the topologies of the environment where the certificates will be installed by scanning the devices, installing and commissioning the certificates.
Logging and Reporting - Producing records of transactions,
- Forwarding these records to the desired places,
- Reporting transactions.
Alarm Generation and System Analysis - Monitoring certificates and predetermining their expiry date,
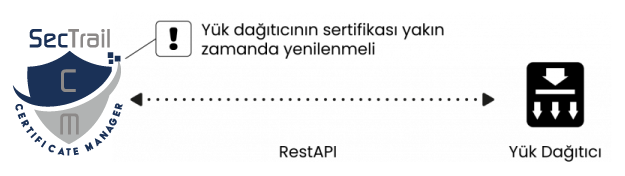
- Generating alarms and notifying them to necessary units.
Multi-Device Integration - Having a wide range of integrations with many devices